Over 90,000 WordPress sites are hacked every day. Most of them had preventable vulnerabilities — outdated plugins, weak passwords, and no security hardening. The good news is that you don’t need to be a developer to protect your site. This guide walks you through 15 proven security hardening steps that dramatically reduce your attack surface and keep hackers out.
Why WordPress Security Matters
WordPress powers over 43% of all websites on the internet, which makes it the single biggest target for hackers. Attacks aren’t personal — they’re automated. Bots continuously scan the web for known vulnerabilities, weak passwords, and unpatched software.
A successful attack can result in your site being used to send spam, mine cryptocurrency, steal customer data, display malicious ads, or simply be taken offline. The cost of recovering from a hack — lost traffic, lost trust, cleanup time, and potential legal liability — far outweighs the time it takes to harden your site today.
Step 1: Keep WordPress, Themes, and Plugins Updated
The number one cause of WordPress hacks is outdated software. The moment a vulnerability is disclosed for a plugin or theme, bots begin scanning for sites still running the vulnerable version. Enable automatic background updates for minor WordPress releases and keep an eye on major version releases.
To enable automatic updates for plugins, go to Dashboard → Updates → Plugins and enable auto-updates for trusted plugins. For themes, do the same in Dashboard → Updates → Themes.
Step 2: Use Strong, Unique Passwords
Brute-force attacks account for a significant percentage of WordPress hacks. Use a password manager (Bitwarden, 1Password, Dashlane) to generate and store unique 20+ character passwords for your WordPress admin, hosting control panel, FTP, and database. Never reuse passwords across accounts.
Step 3: Enable Two-Factor Authentication (2FA)
2FA adds a second layer of protection beyond your password. Even if a hacker obtains your password, they can’t log in without the second factor. Use a plugin like WP 2FA or Two Factor Authentication (from the WordPress.org plugin directory) to add authenticator app support to your login page.
Step 4: Change the Default Admin Username
Many WordPress installations still use “admin” as the administrator username — which means brute-force bots only need to guess the password. If your admin username is “admin”, create a new administrator account with a unique username, then delete the original “admin” account and reassign its content to the new user.
Step 5: Limit Login Attempts
By default, WordPress allows unlimited login attempts. This makes brute-force attacks possible. Install Limit Login Attempts Reloaded or use a security plugin like Wordfence to lock out IP addresses after a set number of failed login attempts (typically 3–5).
Step 6: Install a WordPress Security Plugin
A dedicated security plugin is your all-in-one security toolkit. The top options are:
- Wordfence Security — Includes a WAF (Web Application Firewall), malware scanner, login security, and live traffic monitoring. The free version is excellent.
- Solid Security (formerly iThemes Security) — Great for hardening settings, 2FA, and vulnerability scanning.
- Sucuri Security — Best for malware removal and site monitoring. Pairs with Sucuri’s cloud WAF.
Step 7: Enable a Web Application Firewall (WAF)
A WAF filters malicious traffic before it reaches your server. Cloudflare’s free tier provides basic firewall rules and DDoS protection. For more comprehensive protection, Wordfence’s application-level WAF blocks common WordPress-specific attack patterns like SQL injection, XSS, and file inclusion attacks.
Step 8: Force HTTPS with an SSL Certificate
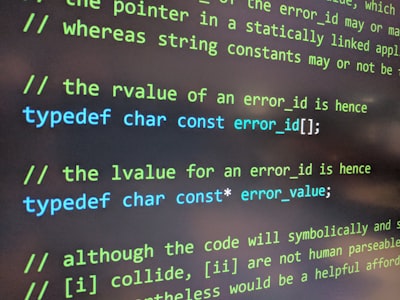
All data between your site and visitors should be encrypted. Install a free SSL certificate via Let’s Encrypt (most hosts provide this in one click) and force all traffic to HTTPS. Add this to your wp-config.php:
define('FORCE_SSL_ADMIN', true);Also add HTTPS redirects in your .htaccess file or use a plugin like Really Simple SSL.
Step 9: Protect wp-config.php and .htaccess
wp-config.php contains your database credentials and secret keys — it must never be publicly accessible. Add this to your .htaccess file to deny direct access:
<Files wp-config.php>
order allow,deny
deny from all
</Files>
<Files .htaccess>
order allow,deny
deny from all
</Files>Step 10: Disable XML-RPC (If Not Needed)
XML-RPC is a WordPress feature that allows remote connections — but it’s frequently exploited for brute-force and DDoS attacks. Unless you’re using a mobile app or Jetpack that requires it, disable XML-RPC. Add this to your .htaccess:
<Files xmlrpc.php>
order deny,allow
deny from all
</Files>Step 11: Hide Your WordPress Version
WordPress displays its version number in the page source code by default. This tells attackers which vulnerabilities to target. Add this to your theme’s functions.php to remove the version number:
remove_action('wp_head', 'wp_generator');Step 12: Set Correct File Permissions
Incorrect file permissions can allow malicious scripts to modify your WordPress files. The recommended permissions are:
| File/Folder | Recommended Permission |
|---|---|
| wp-config.php | 400 or 440 |
| WordPress files (.php) | 644 |
| Directories (wp-content, etc.) | 755 |
| wp-admin directory | 755 |
Step 13: Regularly Back Up Your Site
Backups are your ultimate recovery option. Even with perfect security, no site is 100% unhackable. Set up automated daily backups stored in a remote location (Google Drive, Dropbox, Amazon S3). Use UpdraftPlus (free) or BackupBuddy (premium) for automated off-site backups.
Step 14: Monitor for Malware and Suspicious Activity
Set up active monitoring so you know the moment something goes wrong. Enable Wordfence’s email alerts for admin user creation, failed logins, and file changes. Use Google Search Console which will alert you if Google detects malware on your site. Consider a service like Sucuri SiteCheck for periodic external scans.
Step 15: Choose a Security-Focused Hosting Provider
Your hosting provider is your first line of defense. A good managed WordPress host provides server-level firewall rules, malware scanning, DDoS protection, and automatic patching of server software. Look for hosts that offer:
- Automatic malware removal
- Server-level firewalls
- Isolated hosting environments (so other sites on the server can’t affect yours)
- Automatic WordPress core updates
- Regular security audits
WordPress Security Checklist (Quick Reference)
| Security Step | Difficulty | Impact |
|---|---|---|
| Keep WP/plugins/themes updated | Easy | Very High |
| Strong unique passwords | Easy | High |
| Enable 2FA | Easy | Very High |
| Change admin username | Easy | Medium |
| Limit login attempts | Easy | High |
| Install security plugin | Easy | Very High |
| Enable WAF | Medium | Very High |
| Force HTTPS | Easy | High |
| Protect wp-config.php | Medium | High |
| Disable XML-RPC | Medium | Medium |
| Hide WP version | Easy | Low |
| Set file permissions | Medium | High |
| Set up backups | Easy | Critical |
| Monitor for malware | Easy | High |
| Security-focused hosting | Medium | Very High |
Frequently Asked Questions
How do I know if my WordPress site has been hacked?
Common signs include: unexpected admin users, your site redirecting visitors to spam sites, Google Search Console showing security warnings, your hosting provider suspending your account, or visitors seeing malware warnings in their browsers. Run a free scan at sitecheck.sucuri.net if you suspect a compromise.
Is WordPress secure out of the box?
WordPress core itself is regularly audited and is reasonably secure. The vast majority of WordPress hacks happen through vulnerable third-party plugins and themes, weak passwords, and misconfigured hosting environments — not through WordPress core vulnerabilities.
Final Thoughts
WordPress security hardening doesn’t require advanced technical knowledge — it requires consistency and attention. Work through these 15 steps and you’ll have a site that’s significantly more resistant to attack than the average WordPress installation. Remember: security is not a one-time task. Set up monitoring, keep software updated, and review your security posture every few months.
Need help implementing these security measures? Our WordPress Security & Hardening service starts at $349 and includes a comprehensive audit, full hardening implementation, and a 30-day monitoring period.